Erase the Jeefo virus from your computer by turning to this lightweight software solution that can be operated even by inexperienced users. #Jeefo antivirus #Jeefo remover #Jeefo cleaner #Jeefo #Antivirus #Remover
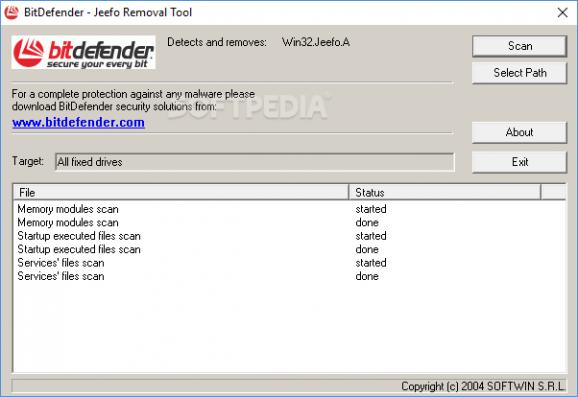
Jeefo Removal Tool is a lightweight utility that can help you clean the Win32.Jeefo.A malware from your system in a quick and uncomplicated manner, making this tool easy to use even by inexperienced users.
Jeefo is an executable file infector that is written in MinGW and presents a very interesting (and difficult to disinfect) infection technique. It contains various strings, encrypted with a trivial algorithm. These include:
.text:004012B0 decryption_loop: .text:004012B0 mov cl, [edx+ebx] .text:004012B3 dec cl .text:004012B5 mov [edx+eax], cl .text:004012B8 inc edx .text:004012B9 cmp edx, edi .text:004012BB jl short decryption_loop
When an infected file is executed for the first time, Jeefo takes control and dumps a copy of itself in the Windows directory as svchost.exe and registers itself to be executed at every system startup.
This way, it makes sure that users won't be able to delete it no matter what, since svchost.exe is a vital component of a healthy operating system. Under older operating systems such as Windows 9x/Me it adds a key to HKEY_LOCAL_MACHINE \Software\Microsoft\Windows\CurrentVersion\RunServices; under NT/2000/XP, it creates a service called "Power Manager".
Jeefo Removal Tool helps by decrypting the file chunks, re-links the original file, adds the resources and relocates them to the new relative virtual address.
- runs on:
- Windows All
- file size:
- 58 KB
- filename:
- antijeefo-en.exe
- main category:
- Antivirus
- developer:
Windows Sandbox Launcher
7-Zip
ShareX
calibre
paint.net
Microsoft Teams
4k Video Downloader
Bitdefender Antivirus Free
Zoom Client
IrfanView
- Bitdefender Antivirus Free
- Zoom Client
- IrfanView
- Windows Sandbox Launcher
- 7-Zip
- ShareX
- calibre
- paint.net
- Microsoft Teams
- 4k Video Downloader