A lightweight application that you can use to immediately detect the presence of the Computrace / Lojack spyware on your laptop or desktop PC. #Lojack finder #Computrace checker #Remove Lojack #Lojack #Computrace #Remove
Computrace Lojack Checker is intended to help you discover traces of the Computrace Lojack anti-theft mechanism on your system. Studies have shown that while this technology can prove extremely useful in determining the location or a stolen computer, its functioning mode might be exploited by cyber criminals to gain remote control over the PC.
The application is very easy to work with and aims to detect the presence of the Computrace Agent within the system registry. No installation is required, so you can access it in an instant.
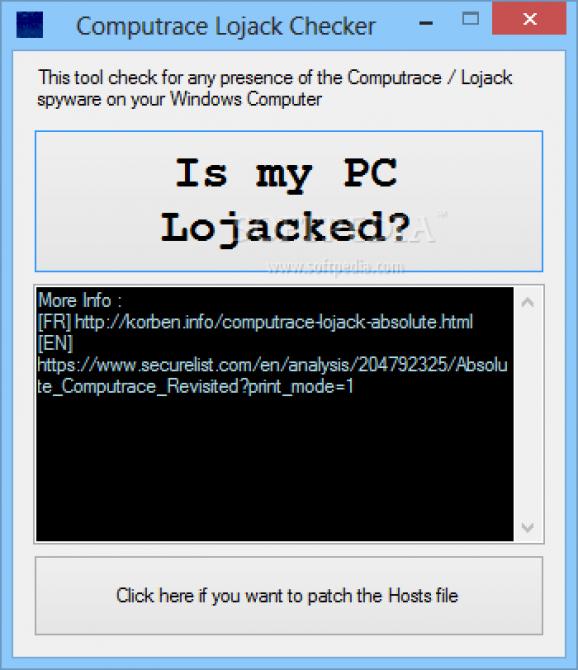
Its interface is simple, comprising one button designed to answer a single question: is your PC 'lojacked' or not? Pressing it instructs Computrace Lojack Checker to start analyzing the system registry and the running processes, in order to identify traces of Lojack.
If the Computrace Agent is launched on your computer, the registry should contain the 'rpcnet' and the 'rpcnetp' services and processes with the same name should be running. If such entries are not found in the registry, the application shows you a message stating that no surveillance traces are found and that everything is fine.
In addition to analyzing the registry and the running processes, Computrace Lojack Checker can also edit the HOSTS file of your PC so as to block all communications between the local system and the Computrace servers. This should actually be the first step to take if the aforementioned registry entries are found.
While the Computrace anti-theft mechanism is a great tool when used solely for finding the location of a stolen PC, its security vulnerabilities and the principles it relies on can turn it into a dangerous exploitation instrument.
The purpose of Computrace Lojack Checker is not to remove the Computrace Agent, but to find indicators of its activity. As such, this application only checks your registry and launched processes so as to find symptoms of the Lojack agent. The only active measure it takes is related to editing the HOSTS file so as to block data sent to the Computrace servers.
Computrace Lojack Checker 1.2
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 8 32/64 bit
Windows 7
Windows Vista
Windows XP - file size:
- 162 KB
- filename:
- Computrace Lojack Checker_1.2.exe
- main category:
- Antivirus
- developer:
- visit homepage
ShareX
Windows Sandbox Launcher
Zoom Client
Context Menu Manager
calibre
IrfanView
Microsoft Teams
Bitdefender Antivirus Free
7-Zip
4k Video Downloader
- Bitdefender Antivirus Free
- 7-Zip
- 4k Video Downloader
- ShareX
- Windows Sandbox Launcher
- Zoom Client
- Context Menu Manager
- calibre
- IrfanView
- Microsoft Teams