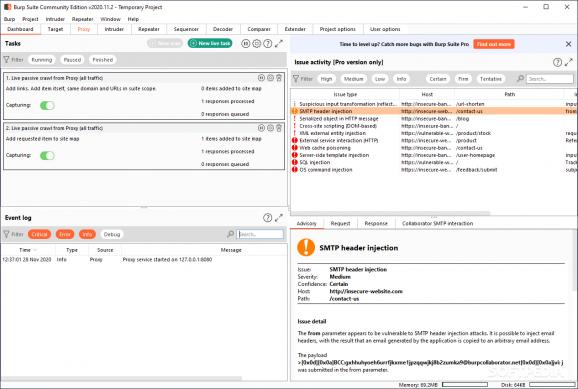
An integrated platform specially intended for users who need to perform security testing of web applications, while crawling content and functionality. #Attack application #Intercept attack #Configure attack #Attack #Scanner #Intruder
Burp Suite is a reliable and practical platform that provides you with a simple means of performing security testing of web applications. It gives you full control, letting you combine advanced manual techniques with various tools that seamlessly work together to support the entire testing process.
The utility is easy-to-use and intuitive and does not require you to perform advanced actions in order to analyze, scan and exploit web apps. It is highly configurable and comes with useful features to assist experienced testers with their work.
The main window displays all the available tools you can choose from and set each one’s settings the way you want.
Being designed to work alongside your browser, the application functions as an HTTP proxy, thus all the HTTP/s traffic from your browser passes through the utility. This way, if you want to perform any kind of testing, you need to configure the browser to work with it.
The first thing you need to do is to confirm that the app’s proxy listener is active. Simply navigate to the Proxy tab and take a look in the Proxy Listeners section. You should see an entry in the table with the Running check box ticked. The second thing you are required to do is to configure your browser to use the app’s proxy listener as its HTTP proxy server. Finally, you need to configure the browser to be able to send HTTP requests through the app without problems.
The previously mentioned utility gives you complete control over all the actions you want to perform and get detailed information and analysis about the web applications you are testing. Using tools such as Intruder, Repeater, Sequencer and Comparer you are able to carry out different actions with ease.
With the help of Spider, you can crawl an application to locate its content and functionality. You are able to add new scope by selecting the protocol and specifying the host name or the IP range. Then the utility monitors all the transferred bytes and queued requests.
The Intruder tool enables you to perform attacks against web apps. Simply set the host name and the port number, define one or more payload sets and you are done. You can also use the HTTP protocol by checking the proper box from the Target tab.
Another tool that automates testing tasks is called Sequencer, which analyzes the quality of randomness in an application’s session tokens. Firstly, you need to load at least 100 tokens, then capture all the requests.
Overall, Burp Suite Free Edition lets you achieve everything you need, in a smart way. It helps you record, analyze or replay your web requests while you are browsing a web application.
What's new in Burp Suite 2024.3.1.2 Early Adopter:
- This release upgrades Burp's built-in browser to Chromium 123.0.6312.122 for Windows and Linux, and 123.0.6312.123 for Mac.
Burp Suite 2024.2.1.5 / 2024.3.1.2 Early Adopter
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 11
Windows 10 64 bit
Windows 8 64 bit - file size:
- 304 MB
- main category:
- Internet
- developer:
- visit homepage
4k Video Downloader
Microsoft Teams
IrfanView
Bitdefender Antivirus Free
paint.net
Zoom Client
calibre
7-Zip
Windows Sandbox Launcher
ShareX
- 7-Zip
- Windows Sandbox Launcher
- ShareX
- 4k Video Downloader
- Microsoft Teams
- IrfanView
- Bitdefender Antivirus Free
- paint.net
- Zoom Client
- calibre