A fast passcode decrypting utility that was designed to help users test the strength of their passwords or recover lost passphrases. #Password cracker #Crack password #Password hash #Password #Crack #Hash
Creating strong passwords seems like an easy task at first glance, but it may actually take more than one would expect. Since there are many programs specially created to break such locks, it's probably a good idea to actually test the strength of a passcode before using it.
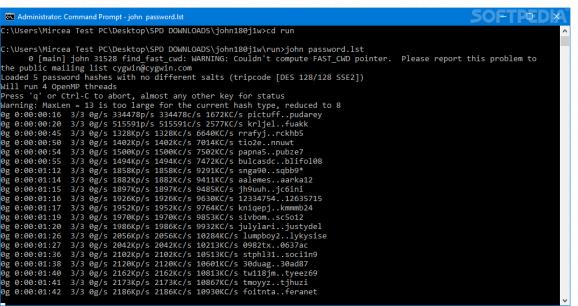
A tool that is quite useful for this purpose is John the Ripper, a command-line utility that will also show its worth in case you need to recover a lost passkey. Since it doesn't have a GUI of its own, you will have to open a Command window and run it from there to view the parameters which can be used to carry out the process.
The actual usage procedure is quite easy and you will have to follow a simple syntax which starts with the executable of, followed by the desired options and then by the password files.
There are several modes in which this application can work, starting with the 'single crack' method, followed by the word list and 'incremental' ones. It is also possible to employ a so-called 'external' mode which acts like a word filter. When using John the Ripper for testing purposes, you can run the benchmarks for a specific time by providing manually the appropriate value.
A great thing about this tool is that you will be able to save sessions and restore them when necessary, using their corresponding parameters. The status of these sessions can even be printed and you also have the possibility to have the deciphered passwords displayed.
All things considered, John the Ripper could actually be one of the better choices whenever someone needs to recover a password or assess the strength of a new one without having to go through a whole series of configurations. Nonetheless, the lack of a proper interface and of more functions may certainly deter some users from utilizing it.
Download Hubs
John the Ripper is part of these download collections: Password Unlockers
John the Ripper 1.9.0 Jumbo 1
add to watchlist add to download basket send us an update REPORT- runs on:
- Windows All
- file size:
- 62.3 MB
- filename:
- john-1.9.0-jumbo-1-win32.zip
- main category:
- Security
- developer:
- visit homepage
Bitdefender Antivirus Free
paint.net
7-Zip
Windows Sandbox Launcher
Microsoft Teams
ShareX
calibre
Zoom Client
4k Video Downloader
IrfanView
- Zoom Client
- 4k Video Downloader
- IrfanView
- Bitdefender Antivirus Free
- paint.net
- 7-Zip
- Windows Sandbox Launcher
- Microsoft Teams
- ShareX
- calibre