Protect shareware applications using several obfuscation tools that keep you source code safe from reverse engineering tasks, as well as compress code data. #Obfuscate code #Protect application #Application obfuscation #Obfuscate #Protect #Convert
Code Virtualizer is a small software application developed specifically for helping developers protect code areas against reverse engineering. The utility is able to scramble code data and transform it into a format that it cannot be read and interpreted by other users.
This is a portable app. You can store it on USB flash drives or other portable devices to have it with you all the time. You may run it without administrative privileges.
Gaining access to its features requires only opening the executable file because there’s no setup included in the process. It does not write entries to your Windows registry and leave other configuration files on the target PC. It actually saves the settings data to the storage device. Getting rid of it implies a simple deletion task of the files that you have downloaded from the Internet.
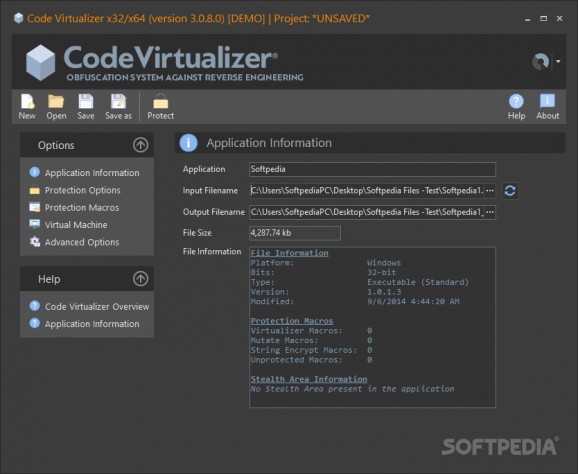
Code Virtualizer reminds of Vista looks and implements several dockable panels which provide quick access to the configuration parameters.
A help manual is included in the package, but we were unable to access it on Windows 10. The feature package is quite straightforward so you are not going to invest a lot of time into the tweaking process.
Code Virtualizer offers you the possibility to provide details about the name of the program and version, pick the executable file (e.g. EXE, OCX, DLL, SCR), and specify the saving directory or save files to the source folder.
You may also view details about the file size, type, and last modified date. Projects can be saved to a file on your computer so you can import them in the future.
What’s more, you are allowed to configure several virtual machines, tweak protection macros (you may read data directly from MAP files), insert the protection code in the last/new section or activate a stealth mode, virtualize strings, compress code, strip relocations, and enable a fake stack simulation mode.
All things considered, Code Virtualizer comes packed with several handy obfuscations tools that help you fight against reverse engineering for protecting shareware applications.
What's new in Code Virtualizer 3.1.8.0:
- Improved detection of false strings in STR_ENCRYPT protection macros
- x64: Improved support for try/catch inside virtualization markers
- Added Advanced Option "OPTION_PROTECTION_DONT_PRESERVE_SECTIONS_FLAGS"
- Improved restoration of GUI windows positions when a monitor has been disconnected
Code Virtualizer 3.1.8.0
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 11
Windows 10 64 bit - file size:
- 29.5 MB
- filename:
- CVdemo.zip
- main category:
- Security
- developer:
- visit homepage
Zoom Client
7-Zip
calibre
Windows Sandbox Launcher
4k Video Downloader
Context Menu Manager
IrfanView
Bitdefender Antivirus Free
Microsoft Teams
ShareX
- Bitdefender Antivirus Free
- Microsoft Teams
- ShareX
- Zoom Client
- 7-Zip
- calibre
- Windows Sandbox Launcher
- 4k Video Downloader
- Context Menu Manager
- IrfanView