A powerful solution for protecting a network and filtering all data traffic to make sure no unauthorized attempts to access the PCs gets through. #Firewall Protection #Intrusion Blocker #Block Intruder #Firewall #Protect #Block
Considering that any PC connecting to the Internet becomes vulnerable to attacks, the importance of having a firewall cannot be stressed enough. Not only does a firewall enhance the protection against malware and hackers, but it also can help improve privacy, as many of the aspects of your connection can be blocked. RusRoute is a dedicated firewall solution that can help protect your computer and LAN from various online threats.
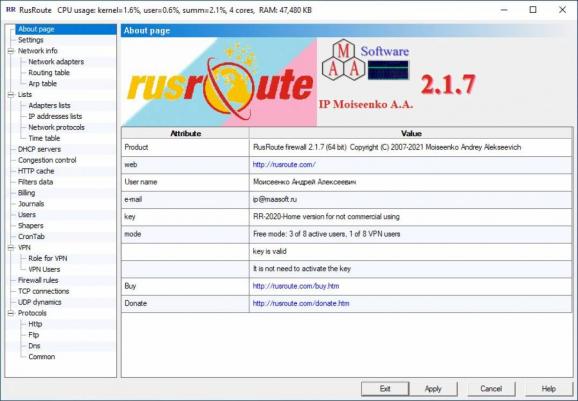
The program comes with a rather minimalistic interface and, judging by the graphical interfaces available today, it does not have a very modern GUI. Nevertheless, the app more than compensates via its functionality.
All available functions and options are available in the single window interface and navigating them entails accessing the drop-down menus. In fact, the tool captures most of the network connection aspects, including, but not limited to flood protection, port scan blocking, VPN client or Ethernet. You should take the time to go through each one of them to configure a safe network environment that can help enhance security and privacy of your home or work computer.
The highlight of the tool stems from the numerous features and options that can be customized to suit your needs and preferences. Regardless of the type of connection, be it HTTPS, DNS, VPN or TCP, the app provides some settings to help you make it more secure.
At the same time, the tool provides comprehensive information about your network and all devices connected. Take note that you can find adapter details for all detected devices in a dedicated List and learn more about IP addresses, time table and network protocols with data about the source, destination, filter or broadcast included.
RusRoute is capable of securing a network environment, while also providing useful features for the management of connected workstations.
What's new in RusRoute 2.8.3:
- Minimal changes related to updating the ToolsLib library (working with files, xml documents, error handling) and supporting the current dump.csv file format (Roskomnadzor blacklist file). We also saved a little processor resources by eliminating unnecessary initializations of IPv6 address objects in the new version of the self-signed driver v.2.07-145 and the RusRoute firewall service and graphical applications.
RusRoute 2.8.3
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 11
Windows 10 64 bit
Windows 8 64 bit
Windows 7 64 bit - file size:
- 15.4 MB
- filename:
- RusRoute_firewall_v2_8_3_x64.exe
- main category:
- Security
- developer:
- visit homepage
Bitdefender Antivirus Free
Microsoft Teams
Windows Sandbox Launcher
Zoom Client
IrfanView
7-Zip
4k Video Downloader
paint.net
ShareX
calibre
- paint.net
- ShareX
- calibre
- Bitdefender Antivirus Free
- Microsoft Teams
- Windows Sandbox Launcher
- Zoom Client
- IrfanView
- 7-Zip
- 4k Video Downloader