Reliable password recovery utility for ZIP archives that have been protected using AES or Zip 2.0 encryption, enabling you to easily retrieve the security key. #Password Recovery #Recover Password #Decrypt ZIP #Password #Recovery #Archive
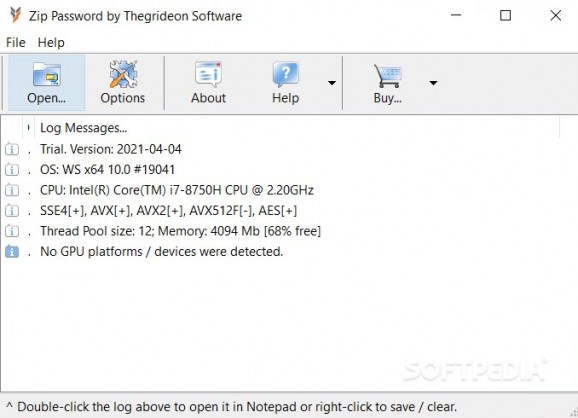
Zip Password comes in handy for situations when you find yourself not being able to open a ZIP archive because the password is either lost or simply forgotten. Using various decryption algorithms, this small utility is capable of retrieving an archive's security key, helping you access its contents afterward.
It works with ZIP, ZIPX and EXE files, but it can only recover passwords for archives that are protected using AES-128, 192 or 256 or Zip 2.0 encryption. Other methods are not supported. For instance, the application returns a 'not a password-protected archive' message for a ZIP file that uses the ZipCrypto algorithm. Extending the list of supported algorithms might add value to this application.
There are several attack methods that can be queued. Practically, if one method does not work, Zip Password uses the next one until it succeeds in retrieving the password.
It features common dictionary attacks with localized wordlists or custom ones, text capitalization and decoding options. Practically, the more letter sequences you remember, the easier is for the application to recover the password.
Brute-force decryption is also an option and, in this case, Zip Password tries combinations of alphabetical and alphanumerical characters to build a word of a certain length, optionally removing duplicates in the charset.
To make sure your password will be retrieved, you can create a mixed algorithm. This method combines the other two, finding the password based on independent parts, wordlists and character combinations.
Using advanced recovery techniques, Zip Password can retrieve passwords of your ZIP files with ease, unprotecting archives and allowing you to browse their content.
Its processing speed depends on the capabilities of your system (especially of the CPU and GPU), as well as other factors, such as the archive content, the compression and the encryption methods, the password length and its complexity. Since computer resources are highly used during recovery, the computer might run slower.
Download Hubs
Zip Password is part of these download collections: Password Unlockers
Zip Password 2022-04-22
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 11
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit - file size:
- 3.8 MB
- filename:
- zpsetup.exe
- main category:
- System
- developer:
- visit homepage
Microsoft Teams
4k Video Downloader
Zoom Client
calibre
7-Zip
ShareX
Context Menu Manager
Bitdefender Antivirus Free
IrfanView
Windows Sandbox Launcher
- Bitdefender Antivirus Free
- IrfanView
- Windows Sandbox Launcher
- Microsoft Teams
- 4k Video Downloader
- Zoom Client
- calibre
- 7-Zip
- ShareX
- Context Menu Manager