A simple to use application that enables you to determine a file's checksum, according to multiple algorithms, then compare it to other hashes. #Calculate Hash #Calculate checksum #Generate Checksum #Hash #Checksum #Calculate
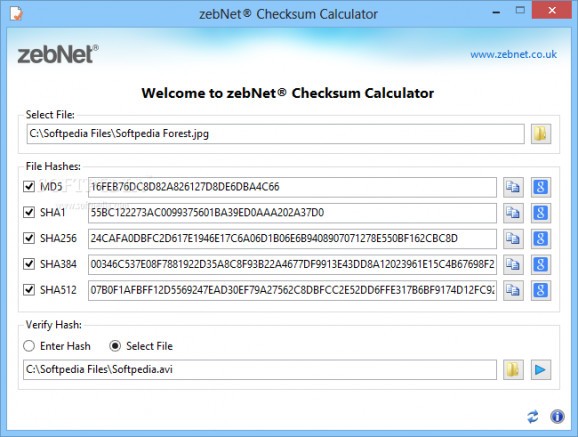
zebNet Checksum Calculator is a reliable application designed to determine the hash for any file, according to multiple algorithms. Thus, it can generate the file’s MD5, SHA1, SHA256, SHA512 and SHA 384 types of checksums.
A file’s hash is a unique identification code, that you can use in order to determine a file’s identity or integrity. When transferring data via the internet, there are several damaging processes that might occur, such as data loss, or acquiring unwanted information. Even the slightest modification can determine the file’s hash to change.
zebNet Checksum Calculator can help you determine this specific identification code for any file, then verify if it matches with the original document. The software can generate hashes for the uploaded file within seconds, according to the selected algorithms. You may choose as many hash calculating formulas as you find necessary, from amongst MD5, SHA1, SHA256, SHA384 or SHA512.
The software allows you to upload a second file, in order to verify the identity of their hashes, or simply paste in the code, if you know it. This implies that the file is already stored on your computer. A dialog box is prompted, in order to notify you if the match is positive or negative.
Alternatively, if you do not own the verification file, or you do not know the hash code, you can easily start a Google search, by clicking the dedicated button next to each algorithm field. This action prompts a Google query, in your browser.
The software features the drag and drop function, that allows you to easily load a file and calculate its hash. It also supports pasting text from clipboard to any field.
zebNet Checksum Calculator can help you determine a file’s hash code, but also compare it to other sources, in order to determine its identity or integrity. Matching hashes is a complementary security check, that allows you to detect if a file has been tampered with and possibly malicious components have been attached to it.
zebNet Checksum Calculator 1.2.3.0
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit
Windows Vista 32/64 bit
Windows XP 32/64 bit - file size:
- 861 KB
- filename:
- checksum_calculator.exe
- main category:
- System
- developer:
- visit homepage
Windows Sandbox Launcher
Microsoft Teams
calibre
7-Zip
paint.net
Bitdefender Antivirus Free
ShareX
IrfanView
Zoom Client
4k Video Downloader
- IrfanView
- Zoom Client
- 4k Video Downloader
- Windows Sandbox Launcher
- Microsoft Teams
- calibre
- 7-Zip
- paint.net
- Bitdefender Antivirus Free
- ShareX