A very useful rootkit scanner and system information utility that keeps common threats at bay while also providing a report on active processes. #Rootkit remover #Detect rootkit #Rootkit scanner #Rootkit #Remover #Remove
IceSword serves to scan your computer for rootkits, continuously monitoring the traffic on the system in order to identify and block potential threats.
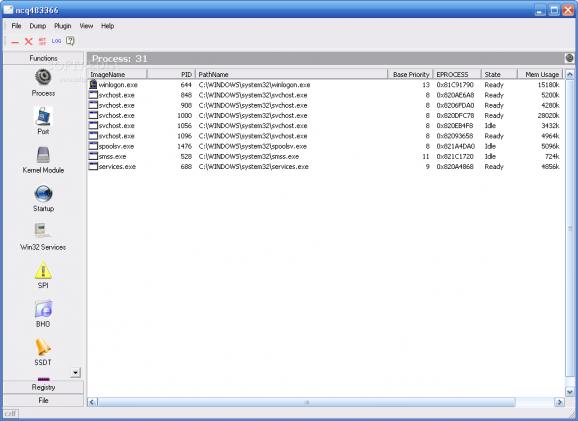
Its secondary purpose is to provide users with an extensive report on the processes running on the PC, including hidden ones that might conceal rootkits or other types of malware.
The program has been on the market for longer than we can remember and unfortunately, has reached a stage where it’s no longer being actively maintained. However, it can still be useful if you’re looking for a quick method of detecting malicious processes.
IceSword delivers a very high amount of information that can be interpreted by more advanced users, thereby it is not aimed at beginners.
It comes inside a portable package, which means it is minimally invasive, leaving the system registry untouched, as opposed to installers which are known to modify several keys.
The interface sports a basic appearance, displaying everything there is to know intuitively, via a sidebar that encases many functions.
As such, you can view process information, with the possibility of halting suspicious entries, access port related details, as well as to trigger an overview of the kernel modules and startup items that are active on your computer.
A scan process is carried out in a fair amount of time, delivering a detailed report of the identified threats, if any.
In addition to these security components, you will also find a registry browser and a file explorer embedded inside the main window.
IceSword may be old and outdated, but still serves its purpose right. The main drawback is that it’s compatible only with Windows 2000, 2003 and XP.
IceSword 1.22
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 2003
Windows XP
Windows 2K - file size:
- 2.4 MB
- filename:
- IceSword.exe
- main category:
- System
- developer:
- visit homepage
Zoom Client
IrfanView
paint.net
Bitdefender Antivirus Free
7-Zip
Windows Sandbox Launcher
Microsoft Teams
4k Video Downloader
calibre
ShareX
- 4k Video Downloader
- calibre
- ShareX
- Zoom Client
- IrfanView
- paint.net
- Bitdefender Antivirus Free
- 7-Zip
- Windows Sandbox Launcher
- Microsoft Teams