Capture the passwords that pass through your network adapter for educational purposes or just for the simple act of pure hacking. #Network sniffer #Capture password #Network capture #Sniffer #Capture #Listen
SniffPass provides you with a rather unorthodox piece of software that capture packets getting through your network interface card and decrypting them in order to display various information on the screen of your computer’s monitor.
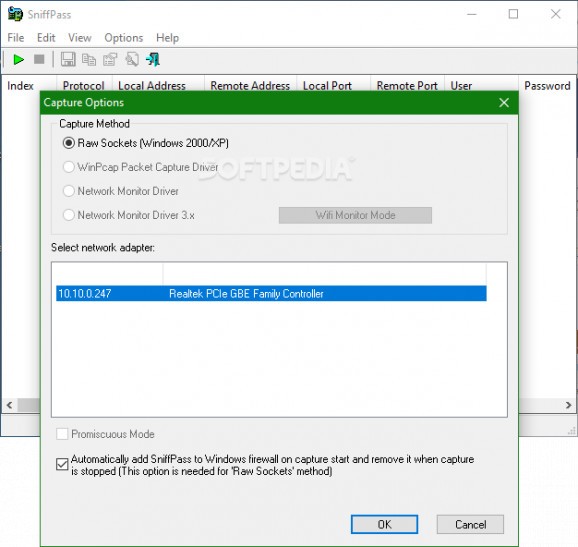
By default, SniffPass requires that you select the method for the capture process to use from options such as raw sockets, WinPcap packet capture driver or other Microsoft specific network monitor drivers. You can also use the promiscuous mode which redirects the network traffic to the CPU (central processing unit or processor), thus enhancing the packet sniffing operation.
This is actually the place where all you have to do really with SniffPass is going down. As long as you find the correct mix of options, the application is surely able to produce data by listening to each and every packet running through the selected NIC. Moreover, SniffPass follows certain protocols such as the ones specific to email servers and clients (POP3 and IMAP for incoming connections as well as the SMTP for outgoing connections).
SniffPass also catches passwords sent through the FTP (File Transfer Protocol) and even HTTP (Hypertext Transfer Protocol). You can also choose to exclude duplicates, make the software beep on any new found password or add a header line to the CSV / tab-delimited file. Due to its nature, SniffPass can trigger various antivirus security threats.
SniffPass does not call for the hacker in you, unless that is the exact reason you have deployed it in the first place. You can also use it for more noble things such as testing out new technologies that keep application such as SniffPass from getting the information within the packet and decrypt it in order to provide an extra layer of protection.
What's new in SniffPass 1.13:
- Fixed bug: When opening the 'Capture Options' dialog-box after Network Monitor Driver 3.x was previously selected, SniffPass switched back to Raw Sockets mode
SniffPass 1.13
add to watchlist add to download basket send us an update REPORT- runs on:
- Windows All
- file size:
- 109 KB
- filename:
- sniffpass_setup.exe
- main category:
- Network Tools
- developer:
- visit homepage
Zoom Client
Windows Sandbox Launcher
Bitdefender Antivirus Free
ShareX
calibre
4k Video Downloader
Microsoft Teams
Context Menu Manager
IrfanView
7-Zip
- Context Menu Manager
- IrfanView
- 7-Zip
- Zoom Client
- Windows Sandbox Launcher
- Bitdefender Antivirus Free
- ShareX
- calibre
- 4k Video Downloader
- Microsoft Teams