A convenient package for anonymous web browsing. #Tor #Proxy server #Communication bouncer #Proxy #Server #Communication
Protecting your privacy when surfing the web is a major challenge nowadays. While using the TCP protocol to connect to the Internet, whether that means web browsing, instant messaging or remote login, you send information regarding your physical location that can sometimes turn against you.
Portable Tor comes to your rescue by bouncing your communications around a network of relays run by a large number of people all around the world. Thus, you prevent anyone from gathering information on web browsing history or any other information referred to as traffic analysis.
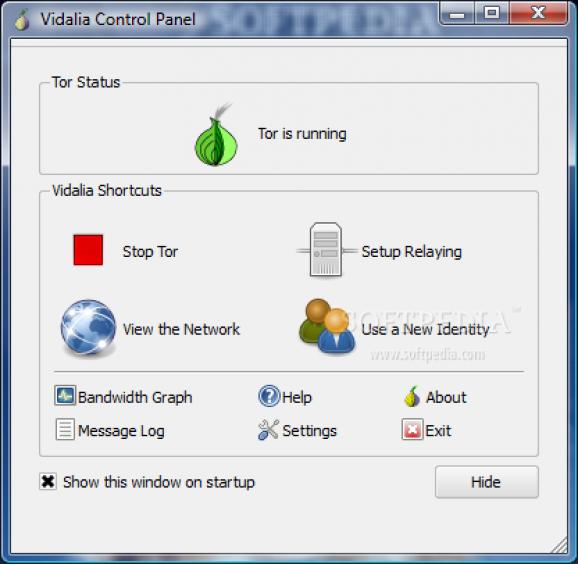
Portable Tor does most of its work without user intervention so the application's interface is kept quite simple. Just start the software and it automatically enables the relay bouncing. If you are curious, you can always view the network of Tor relays and where your traffic is going, by accessing the application's Network Viewer.
Portable Tor also provides users with Bandwidth Usage and Message Log utilities, enabling you to know the exact amount of data that went in and out since the software started or the status information regarding running Tor processes.
If you want to contribute, you can relay traffic for the Tor network, thus becoming a part of the world wide volunteer relay network. You can do this by selecting this option instead of just running the application as a client only.
If you are behind a firewall that only allows you to connect to certain ports, you use a proxy to access the Internet or your ISP is blocking connection to the Tor network, the application has a solution for all of that. All you have to do is specify the connection particularities and Tor immediately redirects your traffic through a series of bridges, unidentifiable by the ISP.
So if you are an activist, law enforcer, journalist, a businessman or just a private person trying to protect your identity and location use Portable Tor to do that by concealing your IP address, whenever and wherever you connect to a public network.
What's new in PortableTor 0.2.1.19-0.1.15-rev0:
- Updated Tor to 0.2.1.19
- Updated Vidalia to 0.1.15
- Modified Privoxy working directory to fix various relative paths
- Included GNU General Public License in .AppDefaultDataPrivoxy folder
PortableTor 0.2.1.19-0.1.15-rev0
add to watchlist add to download basket send us an update REPORT- runs on:
- Windows All
- file size:
- 7.5 MB
- filename:
- PortableTor-0.2.1.19-0.1.15-0.exe
- main category:
- Portable Software
- developer:
calibre
IrfanView
ShareX
Microsoft Teams
7-Zip
4k Video Downloader
Context Menu Manager
Bitdefender Antivirus Free
Zoom Client
Windows Sandbox Launcher
- Bitdefender Antivirus Free
- Zoom Client
- Windows Sandbox Launcher
- calibre
- IrfanView
- ShareX
- Microsoft Teams
- 7-Zip
- 4k Video Downloader
- Context Menu Manager