A lightweight application that enables you to utilize steganography and encrypt sensitive information into your personal image files. #Steganography Encryption #File Encryption #Image Encryption #Encrypt #Encrypter #Steganography
File encryption assures you that no one is able to break the protection and view the information stored into your secured files, but it does not actually hide the data, since the document is still visible and prone to attacks. Hence, a more secure way of transferring encrypted information is necessary, in order to avoid any unwanted attention.
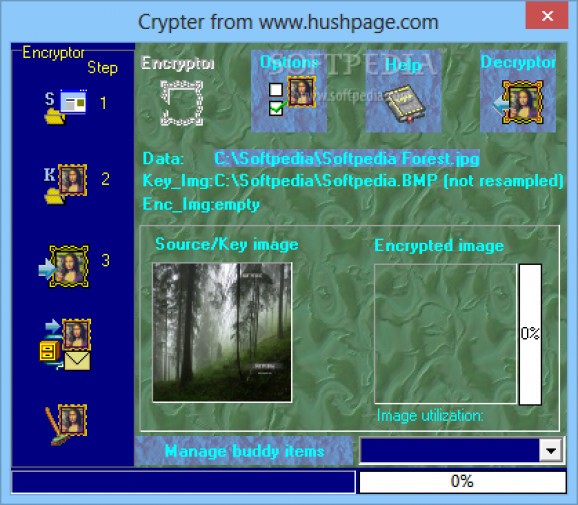
Crypter delivers a solution to this conundrum, by allowing you to use images to hide your data, thanks to an encryption technique called steganography. The procedure involves the storage of small amounts of data directly into the picture's color code, where they are very difficult to trace or even observe without the proper tools and know-how.
In order to achieve this, the application needs two images, one to use as a source and the other to store the decrypted information. The source picture, which is also called a key image, needs to be carefully preserved and saved on your computer, since it is required to perform the decryption process when you need to recover the data.
One of the disadvantages concerning the steganography method is the fact that the resulting images are a couple of times bigger than the original photo, which might raise a few eyebrows, or at least cause you trouble when it comes to email attachments. Crypter, on the other hand, uses a compression technique that keeps the file size to a minimum, while still allowing you to store a decent amount of information inside the pictures.
The source image needs to be resampled before it can be used for decryption and it can be saved under the JPG or BMP formats. Thankfully, the application takes care of the resampling on its own, which enables you to focus on the actual encryption and not worry about how to get the data back when you need it.
Although steganography is a rather complicated and hard-to-follow concept, Crypter makes it seem a bit easier, thanks to the wizard-based interface and the extensive details available for every step. You do, however, still require the appropriate skills in order to take full advantage of the application's full capabilities.
Crypter 1.5.7 Release 7 Build 2
add to watchlist add to download basket send us an update REPORT- runs on:
- Windows All
- file size:
- 1.6 MB
- filename:
- Cryptor.zip
- main category:
- Security
- developer:
- visit homepage
Context Menu Manager
7-Zip
4k Video Downloader
ShareX
Bitdefender Antivirus Free
IrfanView
calibre
Zoom Client
Windows Sandbox Launcher
Microsoft Teams
- Zoom Client
- Windows Sandbox Launcher
- Microsoft Teams
- Context Menu Manager
- 7-Zip
- 4k Video Downloader
- ShareX
- Bitdefender Antivirus Free
- IrfanView
- calibre