A simple to use application that enables you to create and manage encrypted containers that serve as secure storage space for private files. #Encrypt Continer #File Encryption #Access Key #Encrypt #Encryption #Encode
Zed! Free is an intuitive application that enables you to protect private files by creating secure storage spaces. The software can create containers that you can encrypt using a personal access key and password, then generate specific credentials for other authorized users.
Zed! Free can generate encrypted .zed files, in which you may add a large variety of files, with different sizes or formats. The container works like an archive file, that supports a high level of encryption and double verification protocol. Each .zed container depends on a personal access key in the form of a password or a standard certificate, in order to be opened.
The software can generate several different access keys that you can transfer to other authorized users. This way you can make sure that only the selected users can access your protected files. Moreover, a .zed container is a specific format that can only be opened using Zed! Free.
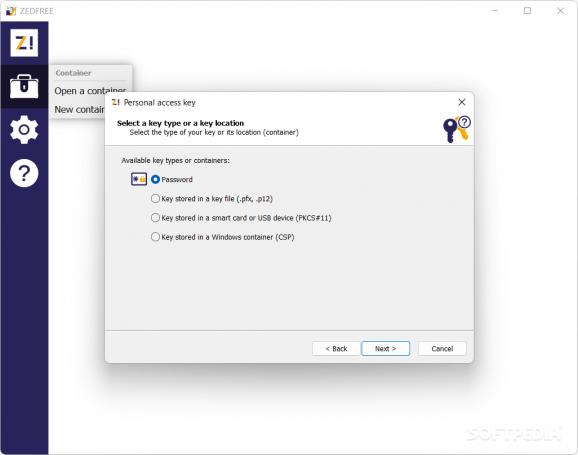
Zed! Free enables you to create secure containers for file transfer, that you can protect by installing a personalized access key for any authorized user. An access key can be a password or a code, stored in a .PFX, .P12 key file, in a smart card, USB device or in a Windows container.
The software uses the AES 128-bit or AES 256-bit encryption types, and it is capable of performing a powerful file compression, without affecting its quality. You may easily add several files to the container, each time you access it, regardless of the size and format of the items. Once you created the container, it is encrypted and ready to be transferred.
With Zed! Free, you may easily create a protected environment for storing files, similar to an archive, that you can safely transfer via the Internet. The software can create pseudo-folders, capable of storing a multitude of files, regardless of the volume. Moreover, you can ensure the container cannot be opened or otherwise tampered with, due to the high level of encryption used by the software.
Zed! Free 2023.5 Build 1
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 11
Windows 10 64 bit
Windows 8 64 bit
Windows 7 64 bit - file size:
- 29.6 MB
- filename:
- Setup ZEDFREE 2023.5 x64.exe
- main category:
- Security
- developer:
- visit homepage
ShareX
4k Video Downloader
IrfanView
7-Zip
Context Menu Manager
Zoom Client
Bitdefender Antivirus Free
calibre
Windows Sandbox Launcher
Microsoft Teams
- calibre
- Windows Sandbox Launcher
- Microsoft Teams
- ShareX
- 4k Video Downloader
- IrfanView
- 7-Zip
- Context Menu Manager
- Zoom Client
- Bitdefender Antivirus Free