Actively protects you from viruses, spam, identity theft and social media dangers and tracks virtually every file on the Internet. #Internet Protection #Antivirus Protection #Vulnerability Detector #Antivirus #Scanner #Detector
Note: Norton Security has been discontinued and replaced by the company's newer product, Norton 360. Follow the buy links to purchase a Norton 360 subscription.
Norton Security represents Symantec's next step in terms of PC safety and malware prevention. For those unfamiliarized with Norton, the software utility is designed to prevent, identify and remove files infected with viruses, Trojans, worms, rootkits and other kinds of malicious traces, in addition to some safety measures concerning online navigation.
Setting up Security should be a fast and painless task to any user, since the tool is not flexible when it comes to handpicking the components; everything is installed by default.
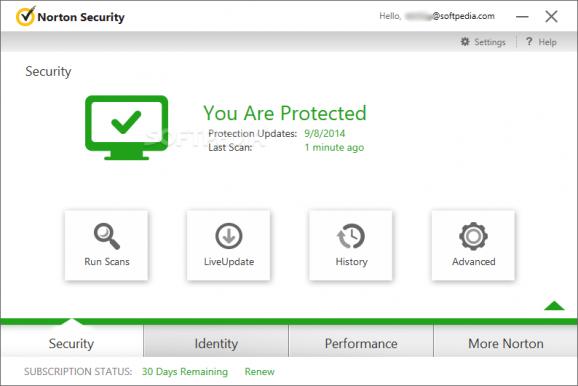
Sharing its look with Norton AntiVirus Plus, Security's interface is mostly user-friendly, although some of its options could have been better put together. Most security modules can be activated and deactivated with one click, as well as configured in detailed by advanced users. Terminology could be an issue in some cases, since Norton adopts unique names to describe proprietary technologies.
Settings may be customized in detail for Norton Security by defining the scanning scope, such as compressed files, rootkits and stealth items, network drives, heuristics protection, low-risk threats, tracking cookies, scan scheduler, file and virus signature exclusions, and so on.
The real-time protection module has all components turned on by default. Norton is able to prevent spyware from infiltrating into the system while keeping an eye out for suspicious removable media devices and network locations. It can also scan Windows autostart entries at every boot sequence and hide notifications to let users carry on with normal PC activity without any intrusions.
All traffic between the computer and other systems can be temporarily blocked, while intrusion signatures can be customized to give passes to any items. The application monitors incoming and outgoing messages in email clients, and also features a personal firewall for network traffic, apps with tailored Internet access rules, and so on.
Online navigation is ensured by Norton, since it oversees web addresses and notifies users on malware-infected or suspicious links. It also keeps track of downloaded files and includes an identity safe to hold all confidential data in one place (e.g. autofill forms, credit card info). What's more, users are protected from phishing websites whose purpose is to steal transactional data.
Thanks to the cloud technology used, Norton Security finishes scan jobs faster than many other av products. It is mostly successful concerning identified and removed malware files, and regularly receives virus definition updates. CPU and RAM consumption is generally low. Although less experienced users are likely to get lost in translation when trying to figure our each features, advanced ones will probably find Norton Security worthwhile.
Download Hubs
Norton Security (Norton 360) is part of these download collections: Parental Controls, Spyware Remover, Trojan Remover, Internet Security Suites
Norton Security (Norton 360) 2020 22.20.5.39
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit - file size:
- 183 MB
- main category:
- Antivirus
- developer:
- visit homepage
IrfanView
7-Zip
ShareX
4k Video Downloader
Context Menu Manager
Bitdefender Antivirus Free
Windows Sandbox Launcher
Zoom Client
Microsoft Teams
calibre
- Zoom Client
- Microsoft Teams
- calibre
- IrfanView
- 7-Zip
- ShareX
- 4k Video Downloader
- Context Menu Manager
- Bitdefender Antivirus Free
- Windows Sandbox Launcher