Identifies possible vulnerabilities of a system that was previously infected by W32/Pinkslipbot and might still be a control server proxy for the malware #Pinkslipbot remover #Pinkslipbot service detector #Pinkslipbot cleaner #Pinkslipbot #Remover #Detector
Also known as Qakbot, Akbot or Qbot, the W32/Pinkslipbot worm uses different propagation vectors. It mainly spreads through infected Internet files that are downloaded locally or network shares. Once it reaches a computer, it can communicate to its command and control center in the attempt to download a backdoor that steals private information about the computer user.
Even if one manages to remove the malware from their computer, it has been discovered that Pinkslipbot uses infected machines as control proxy servers.
Home computers in North America that are behind an address translation router are particularly vulnerable, as the worm takes advantage of the UPnP (Universal Plug and Play) technology to open ports and authorize incoming connections without the user's consent. The proxy components can be downloaded, which results in the creation of new port-forwarding rules. Such changes are difficult to trace and even more difficult to revert by security software, as the risk of network misconfigurations is high. In other words, although users might have managed to remove W32/Pinkslipbot from their systems, the computer might still be prone to outside attacks.
To avoid vulnerabilities that result as a consequence of the PC being infected by Pinkslipbot, McAfee created a specialized software utility that can identify malicious services and eliminate port mappings that might have been created to turn the machine into an HTTP-based control proxy server. Its name is quite long, but it reveals its role entirely. It is called the Pinkslipbot Control Server Proxy Detection and Port-Forwarding Removal Tool.
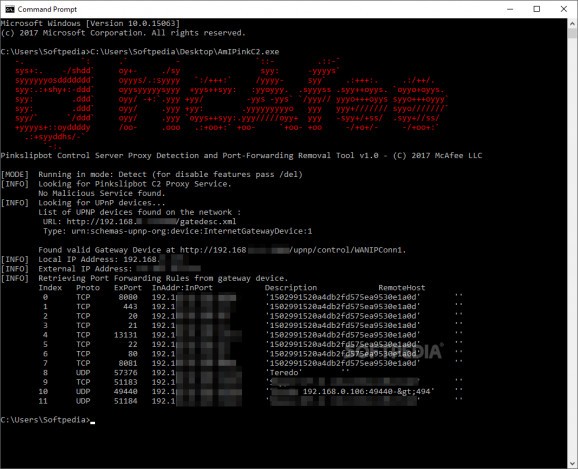
Running in the console only, this application starts in detection mode by default, making no changes to the PC or the network configuration. It can identify the Pinkslipbot C2 proxy service and UPnP devices that might become attack points.
The application shows the user if any malicious service is running on their system and displays a list of all the UPnP devices and gateway services, along with the port forwarding rules on the local machine. To get disabling features one has to pass "/del" as an argument.
McAfee's utility is specifically designed to address the Pinkslipbot malware, using specific indicators to determine if the system is compromised. It identifies the Pinkslipbot control server proxy service if available and disables it upon request. Keep in mind that the service is not completely removed.
Pinkslipbot Control Server Proxy Detection and Port-Forwarding Removal Tool 1.0
add to watchlist add to download basket send us an update REPORT- runs on:
-
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit
Windows Vista 32/64 bit
Windows XP 32/64 bit - file size:
- 88 KB
- filename:
- AmIPinkC2.exe
- main category:
- Antivirus
- developer:
- visit homepage
Zoom Client
7-Zip
Microsoft Teams
4k Video Downloader
ShareX
Context Menu Manager
Windows Sandbox Launcher
calibre
Bitdefender Antivirus Free
IrfanView
- calibre
- Bitdefender Antivirus Free
- IrfanView
- Zoom Client
- 7-Zip
- Microsoft Teams
- 4k Video Downloader
- ShareX
- Context Menu Manager
- Windows Sandbox Launcher