An application to detect vulnerabilities on our network #Software vulnerability #Vulnerability report #Software update #Scan #Vulnerability #Alert
It is not magic (still ...), simply compares the vulnerabilities that it has received from the sources with the software that we have installed on our servers. Those vulnerabilities are stored into the database creating a vulnerability repository.
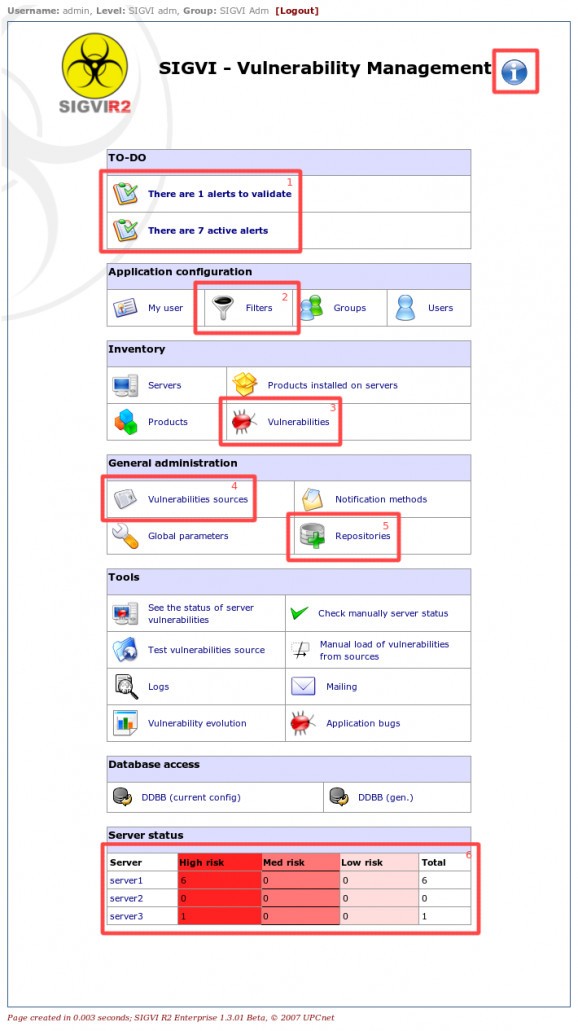
When SIGVI R2 finds a software that is vulnerable, it creates an alert and sends notifications to the administrators of the server.
Here are some key features of "SIGVI R2":
The SIGVI uses vulnerability sources to download / receive the updates of the vulnerabilities. Periodically, the application connect to the sources, using their plugin, get the vulnerabilities and store them into the SIGVI database. Those vulnerabilities are available through one of the pages from SIGVI, with search options. The vulnerability system is based on plugins, so you can define your own sources format inheriting the main source class and write two functions to read and loop rows, but don't worry, because, by default, the application suports the NVD(National Vulnerability Database: nvd.nist.gov) format.
After the vulnerability loading process, SIGVI will send a report of the new or updated vulnerabilities to each user using their filter.
The products that we associate with our servers are stored into a table from the SIGVI database. These products are automatically updated for each new loaded vulnerability (new products are inserted). Initially, the products are downloaded from the NVD products file.
SIGVI needs to know which software is installed on each server to determine when a software is vulnerable. The basic way is doing it manually, so you have to enter the basic services (for example those which are accesible remotely) on each server.
Once the vulnerabilities has been loaded from sources, SIGVI will perform the comparison between the software list of each new vulnerability and the software that we have associated on each server, using the server filter (if any).
For each vulnerability affecting one product on one server, SIGVI creates a new alert. For each alert, SIGVI calculates a Risk Factor, based on the risk properties of the vulnerability (CVSS vector, ...) and the properties of the service (the product on this server).
The filters are used to determine when to notify about a vulnerability and which type of vulnerabilities will be checked on each server.
How notifications are sent is defined by the notifications plugins. By default there is only one: email, but you can define your own, for example to create a ticket on the incidents database of your environment.
All vulnerabilities loaded from SIGVI are inserted into the database, so a vulnerability repository will be accesible with search options. Each row is linked with the definition on the source (NVD) and with the detail of this vulnerability.
SIGVI R2 1.3.02 Beta
add to watchlist add to download basket send us an update REPORT- runs on:
- Windows All
- file size:
- 1.5 MB
- main category:
- Programming
- developer:
- visit homepage
4k Video Downloader
7-Zip
IrfanView
ShareX
Context Menu Manager
Microsoft Teams
Bitdefender Antivirus Free
calibre
Zoom Client
Windows Sandbox Launcher
- calibre
- Zoom Client
- Windows Sandbox Launcher
- 4k Video Downloader
- 7-Zip
- IrfanView
- ShareX
- Context Menu Manager
- Microsoft Teams
- Bitdefender Antivirus Free