Match all your project's dependencies to the open-source OSV database to identify existing vulnerabilities that might impact them. #Vulnerability scanner #Dependency scanner #OSV vulnerability #Vulnerability #Scanner #Dependency
The Open-Source Vulnerability database or, in short, OSV, is an initiative that delivers vulnerability information for the open-source community in OSV format. Aiming to make it easier for developers to find vulnerabilities that might affect their projects, Google created OSV-Scanner, which works as a front-end for the OSV database.
Released under an open-source license itself, OSV-Scanner delivers a powerful console application that can analyze manifest files, commits and software bill of materials (SBOMs) to match any dependencies in the project against the OSV database. This software tool can find the identified vulnerabilities in the distributed OSV database that are related to any of the project files. Needless to say, finding vulnerabilities results in fewer error notifications and a significant reduction in the time needed to address them.
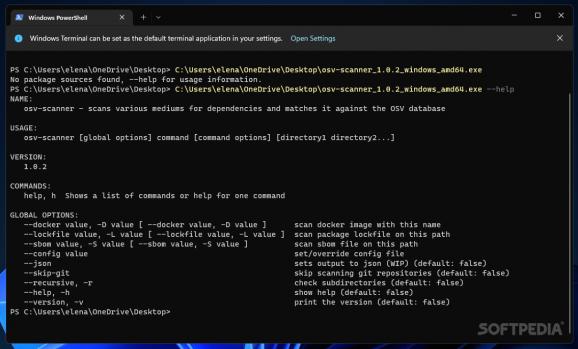
There is no need to install OSV-Scanner, as it is ready for use via the Windows terminal. You can use the “--help” command to see a list of all the actions and details about each.
You can scan docker images, package lockfiles (yarn.lock, composer.lock, Gemfile.lock, go.mod, mix.lock, poetry.lock, requirements.txt, and more) , as well as software bill of materials (SBOMs) files (SPDX and CycloneDX are supported) with OSV-Scanner. When analyzing a project, this small utility can detect all the dependencies that are in use and then query the OSV database to determine any vulnerability associated with the development project. Git repositories can be optionally excluded from the analysis. In recursive mode, OSV-Scanner also scans sub-directories, not just main folders.
About the output, the list of vulnerabilities is shown in tabular format by default, which is human readable. However, you can also configure OSV-Scanner to generate a JSON file containing all the data, as the JSON schema is versatile and machine readable.
Google’s OSV-Scanner can be used by developers who need to interrogate the OSV database to find vulnerabilities that affect their projects. An easy-to-use API is also available for interrogating the database, but a command-line tool such as OSV-Scanner is more convenient to use for scanning SBOM, lockfiles or directories recursively.
What's new in OSV-Scanner 1.7.2:
- Fixes:
- Bug #899 Guided Remediation: Parse paths in npmrc auth fields correctly.
- Bug #908 Fix rust call analysis by explicitly disabling stripping of debug info.
- Bug #914 Fix regression for go call analysis introduced in 1.7.0.
OSV-Scanner 1.7.2
add to watchlist add to download basket send us an update REPORT- PRICE: Free
- runs on:
-
Windows 11
Windows 10 64 bit - file size:
- 28.9 MB
- filename:
- osv-scanner_windows_amd64.exe
- main category:
- Security
- developer:
- visit homepage
Zoom Client
Microsoft Teams
4k Video Downloader
Bitdefender Antivirus Free
ShareX
Context Menu Manager
7-Zip
calibre
IrfanView
Windows Sandbox Launcher
- calibre
- IrfanView
- Windows Sandbox Launcher
- Zoom Client
- Microsoft Teams
- 4k Video Downloader
- Bitdefender Antivirus Free
- ShareX
- Context Menu Manager
- 7-Zip