Reverse-engineering tool that scans running processes for hidden malware by dumping the unpacked code back from the memory to the disk #Malware research #Process analyzer #Analyze process #Process #Dump #Dumper
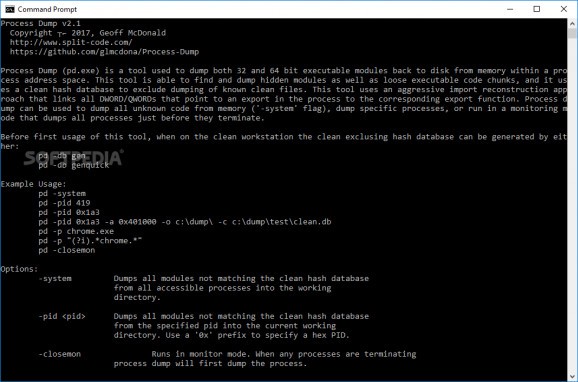
Designed for malware researchers and other security experts, Process Dump is a command-line utility that can reverse-engineer memory components to analyze processes for malware. This is useful for spotting malware files that are packed and concealed before execution, in an attempt to fly under the radar of antivirus scanners. On execution, these files usually unpack or inject the malware code into the memory.
Process Dump offers a solution to inspect malware by dumping the unpacked code back from the memory to the disk, which can be then scanned with regular antivirus applications. It's available for 32-bit and 64-bit processes, doesn't have to be installed, and requires administrative privilege to avoid permission errors during scans.
To get started, it's necessary to create a database with hashes of all processes to set the clean ones aside. Afterward, you can instruct the tool to dump all modules which don't match the clean hashes. You can shift Process Dump's attention to a particular process only and make it run in close monitor mode to make sure that processes get paused and dumped before they are terminated.
The utility is capable of locating and dumping loose code chunks that are not associated with any PE files, and of building a PE header and import table for these chunks. If any issues are encountered in this case, you can apply force when generating the PE headers from scratch (while ignoring existing headers). Otherwise, you can dismiss this entire dumping procedure.
Process Dump takes an aggressive approach toward reconstructing these import tables but can be disabled. You can set the number of threads to use (default is 16) to influence the processing speed or deactivate multi-threading mode if it takes a heavy toll on system resources usage, as well as specify the full path to the clean hash database to use in the current session.
Taking into account the rich commands it provides, Process Dump can be a helpful assistant in identifying malware hidden inside running processes.
What's new in Process Dump 2.1.1:
- Statically link libraries, which removes the pre-install dependency on Microsoft Visual C++ Redistributable per suggestion from Blaine for easier integration to Mandiant FLARE-VM.
Process Dump 2.1.1
add to watchlist add to download basket send us an update REPORT- PRICE: Free
- runs on:
-
Windows 11
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit - file size:
- 479 KB
- filename:
- pd32.exe
- main category:
- Security
- developer:
- visit homepage
ShareX
4k Video Downloader
Context Menu Manager
Windows Sandbox Launcher
Zoom Client
IrfanView
Microsoft Teams
calibre
Bitdefender Antivirus Free
7-Zip
- calibre
- Bitdefender Antivirus Free
- 7-Zip
- ShareX
- 4k Video Downloader
- Context Menu Manager
- Windows Sandbox Launcher
- Zoom Client
- IrfanView
- Microsoft Teams