A Python-based infrastructure scanner that enables you to find hosts that could be affected by the Apache Log4j RCE CVE-2021-44228 vulnerability. #Log4j scanner #Find log4j #Scan for log4j #Log4j #Scanner #Scan
The Log4j vulnerability (CVE-2021-44228) has taken over the Internet in December 2021, as a massive, widespread security flaw had cybersecurity experts racing to find a solution. The high-risk vulnerability affects the open-source logging software provided by the Apache Software Foundation and used by some of the most popular services, games and software tools, hence the madness it generated.
As patches have already been released, financial institutions, government entities and companies worldwide are struggling to upgrade their systems to avoid potential cyber-attacks, especially since Log4j is a remote code execution (RCE) vulnerability that can be exploited to take over the control of computers or entire networks. But before addressing the issue, you have to find the workstations that are affected and that is where log4j-scan comes in.
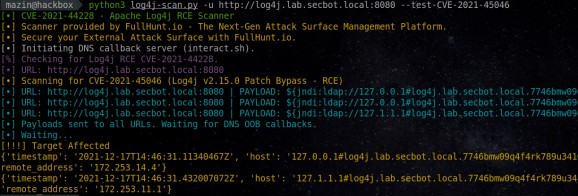
log4j-scan is an open-source scanner and detection tool written in Python that can analyze your entire infrastructure to find hosts that are affected by the Log4j vulnerability. Designed for security experts, this Python script that can find Log4j remote code execution and discover WAF bypass payloads on the environment as well.
The scanner can scan individual URLs or lists of multiple URLs, allowing TXT files as parameters. log4j-scan facilitates fuzzing for more than 60 HTTP request headers, HTTP POST and JSON data parameters. It can scan single URLs using all the requests methods.
It provides support for DNS OOB callbacks. In other words, you don’t have to set up a DNS callback server to use it.
log4j-scan is designed for vulnerability discovery and validation, providing a quick way for security experts to find hosts affected by the Log4j vulnerability.
System requirements
What's new in log4j-scan 1.0.1:
- Added additional 15 community-provided WAF bypass payloads (Total payloads: 23 payloads).
- Added additional common default POST parameters.
- Added --custom-waf-bypass-payload to add user-defined custom WAF bypass payload.
- Fixed a minor exception when "Referer" is not set on the headers-file list.
log4j-scan 1.0.1
add to watchlist add to download basket send us an update REPORT- PRICE: Free
- runs on:
-
Windows 11
Windows 10 32/64 bit
Windows 8 32/64 bit
Windows 7 32/64 bit - file size:
- 5 KB
- filename:
- log4j_scan.zip
- main category:
- Security
- developer:
- visit homepage
Microsoft Teams
IrfanView
4k Video Downloader
7-Zip
Context Menu Manager
Windows Sandbox Launcher
Bitdefender Antivirus Free
Zoom Client
ShareX
calibre
- Zoom Client
- ShareX
- calibre
- Microsoft Teams
- IrfanView
- 4k Video Downloader
- 7-Zip
- Context Menu Manager
- Windows Sandbox Launcher
- Bitdefender Antivirus Free